For RC4 we decided to re-design our configuration object model for resources (formerly known as scopes).
I know, I know – we are not supposed to make fundamental breaking changes once reaching the RC status – but hey – we kind of had our “DNX” moment, and realized that we either change this now – or never.
Why did we do that?
We spent the last couple of years explaining OpenID Connect and OAuth 2.0 based architectures to hundreds of students in training classes, attendees at conferences, fellow developers, and customers from all types of industries.
While most concepts are pretty clear and make total sense – scopes were the most confusing part for most people. The abstract nature of a scope as well as the fact that the term scope has a somewhat different meaning in OpenID Connect and OAuth 2.0, made this concept really hard to grasp.
Maybe it’s also partly our fault, that we stayed very close to the spec-speak with our object model and abstraction level, that we forced that concept onto every user of IdentityServer.
Long story short – every time I needed to explain scope, I said something like “A scope is a resource a client wants to access.”..and “there are two types of scopes: identity related and APIs…”.
This got us thinking if it would make more sense to introduce the notion of resources in IdentityServer, and get rid of scopes.
What did we do?
Before RC4 – our configuration object model had three main parts: users, client, and scopes (and there were two types of scopes – identity and resource – and some overlapping settings between them).
Starting with RC4 – the configuration model does not have scope anymore as a top-level concept, but rather identity resources and API resources.
Image may be NSFW.
Clik here to view.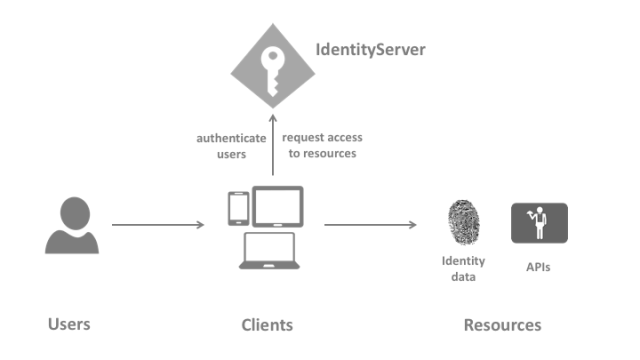
We think this is a more natural way (and language) to model a typical token-based system.
From our new docs:
User
A user is a human that is using a registered client to access resources.
Client
A client is a piece of software that requests tokens from IdentityServer – either for authenticating a user (requesting an identity token)
or for accessing a resource (requesting an access token). A client must be first registered with IdentityServer before it can request tokens.
Resources
Resources are something you want to protect with IdentityServer – either identity data of your users (like user id, name, email..), or APIs.
Enough talk, show me the code!
Pre-RC4, you would have used a scope store to return a flat list of scopes. Now the new resource store deals with two different resource types: IdentityResource and ApiResource.
Let’s start with identity – standard scopes used to be defined like this:
public static IEnumerable<Scope> GetScopes() { return new List<Scope> { StandardScopes.OpenId, StandardScopes.Profile }; }
..and now:
public static IEnumerable<IdentityResource> GetIdentityResources() { return new List<IdentityResource> { new IdentityResources.OpenId(), new IdentityResources.Profile() }; }
Not very different. Now let’s define a custom identity resource with associated claims:
var customerProfile = new IdentityResource( name: "profile.customer", displayName: "Customer profile", claimTypes: new[] { "name", "status", "location" });
This is all that’s needed for 90% of all identity resources you will ever define. If you need to tweak details, you can set various properties on the IdentityResource class.
Let’s have a look at the API resources. You used to define a resource-scope like this:
public static IEnumerable<Scope> GetScopes() { return new List<Scope> { new Scope { Name = "api1", DisplayName = "My API #1", Type = ScopeType.Resource } }; }
..and the new way:
public static IEnumerable<ApiResource> GetApis() { return new[] { new ApiResource("api1", "My API #1") }; }
Again – for the simple case there is not a huge difference. The ApiResource object model starts to become more powerful when you have advanced requirements like APIs with multiple scopes (and maybe different claims based on the scope) and support for introspection, e.g.:
public static IEnumerable<ApiResource> GetApis() { return new[] { new ApiResource { Name = "calendar", // secret for introspection endpoint ApiSecrets = { new Secret("secret".Sha256()) }, // claims to include in access token UserClaims = { JwtClaimTypes.Name, JwtClaimTypes.Email }, // API has multiple scopes Scopes = { new Scope { Name = "calendar.read_only", DisplayName = "Read only access to the calendar" }, new Scope { Name = "calendar.full_access", DisplayName = "Full access to the calendar", Emphasize = true, // include additional claim for that scope UserClaims = { "status" } } } } };
IOW – We reversed the configuration approach, and you now model APIs (which might have scopes) – and not scopes (that happen to represent an API).
We like the new model much better as it reflects how you architect a token-based system much better. We hope you like it too – and sorry for moving the cheese ;)
As always – give us feedback on the issue tracker. RTM is very close.
Filed under: .NET Security, ASP.NET, OAuth, Uncategorized, WebAPI Image may be NSFW.
Clik here to view.
Clik here to view.
Clik here to view.
Clik here to view.
Clik here to view.
Clik here to view.
Clik here to view.
Clik here to view.